Just a couple of weeks ago, ConsenSys announced several changes to its privacy policy, which affected one of its most popular products - Metamask, the most widely used cryptocurrency wallet for traversing the multiverse of EVM-based networks. Most notably, the announcement included an update mentioning that Infura, Metamask’s default RPC provider for Ethereum (also owned by ConsenSys), collects information about users’ IP and wallet addresses whenever the application is used to perform transactions. Additionally, there were claims that these wallet addresses under the same IP address will also be recorded right from the moment that the MetaMask wallet is unlocked.
Understandably, Crypto Twitter went into a frenzy when the news broke. Many were outraged and quick to voice out their concerns about their loss of privacy, especially when anonymity is one of the very core features that the crypto space offers. The phrase ‘not your keys, not your coins’ is more relevant than ever following the demise of multiple centralized crypto services, as well as the U.S. increasing its regulatory activity. Users have become more aware of the importance of taking charge of their own funds across the wild west of decentralized networks without the need to expose their identity.
Given MetaMask and Infura are the dominant wallet and RPC for EVM chains, every move they make is examined under a microscope as it will affect a significant portion of the crypto community. But what exactly was the reasoning behind their latest update, what’s going to happen moving forward, and do users have any other options to maintain their privacy? Let’s dig in!
So, What’s Going On?
On November 23rd, ConsenSys updated several clauses in its privacy policy to better illustrate the type of information collected from users and how they were being handled. Although it was always stated that the collection of sensitive data may include contact information and transaction information, a new addition to the policy was the type of data that Infura could retrieve from MetaMask users. The latest changes to the policy sent alarm bells ringing across the community that their privacy was at risk.
In response to the backlash, the ConsenSys team has since released an initial statement on the recent changes, clarifying that their policy had always stated that certain information, such as IP addresses, were automatically collected each time a user interacts with their products. According to the team, the sole purpose of adding the particular clause on Infura was to provide higher transparency to users, ensuring that they are informed of how information is collected and used when they interact with the blockchain through MetaMask and Infura.
To be more specific, IP data is automatically logged simply based on how the app’s architecture is structured, and this is not a behaviour that is specific to Infura alone but the majority of web apps. Besides that, the data is used to ensure that transactions are properly broadcasted and executed onto the Ethereum network, in addition to other important functions for Infura to operate smoothly, such as load balancing and DDoS protection.
Additionally, the updated policy will not result in a more intrusive experience for users and was not influenced by regulatory demands. In other words, nothing has changed other than the language of the policy. For the smooth functioning of the app, some level of data has always been collected during the course of users’ interactions with MetaMask and Infura.
Besides that, they have made it clear that Infura will only gather your data when it is used as the default RPC provider in MetaMask. If you switch to another RPC provider or host their own endpoint, then neither your IP address nor your Ethereum address will be retrieved by MetaMask or Infura. However, your information may still be collected by third-party RPC providers, where the usage of such data by the provider is dependent on their own terms and conditions, which may be even more hidden and invasive.
Dan Finlay, one of the co-founders of MetaMask, has also taken to Twitter to address some of the concerns surrounding these changes. Reinforcing ConsenSys’ official stance on the issue, Finlay reasserts that MetaMask has not and will not pivot towards implementing increased surveillance in its products but simply promoting greater transparency while remaining compliant with law enforcement. Finlay also mentioned that they are looking to store as little personal data as possible while the team actively works on providing more private and secure solutions.
Further Updates from ConsenSys
Following feedback from the community, Consensys has since released an update on their data retention policies, highlighting several key issues on how data is stored by Infura and MetaMask, as well as several planned upgrades for improving privacy. Below are some of the key points:
1. When users unlock their wallets to check their account balances on MetaMask, both IP addresses and wallet addresses are never recorded. For users who perform transactions, wallet data and IP addresses are stored separately, such that they cannot be associated with one another.
2. Wallet and IP information is only retained for a short period of time before they are deleted. ConsenSys has stated that they will improve on cutting retention time to 7 days, which will be reflected in a future policy update.
3. ConsenSys will be updating MetaMask to promote greater control among users. A new advanced settings page will allow new users to choose their own RPC providers upon setup and to opt out of additional third-party services. Additionally, a user’s personal settings will not be overridden or reverted back to the default, and custom RPC selection will be revamped to become more user-friendly and to prevent a false sense of non-security.
What Can You Do to Preserve Your Privacy?
If you’re still not too happy about these recent changes, there are a few alternatives and additional measures that you can take to continue maintaining your privacy across decentralized networks. And even if you don't feel too strongly about ConsenSys’ actions, some of these tips will still go a long way in boosting your security and protecting you and your transactions from being doxxed. In no particular order, here are some suggestions to help you preserve your privacy across the multichain cryptoverse.
1. Using a VPN
Probably one of the easier ways of protecting your internet traffic and masking your IP address is to install a proper VPN or virtual private network on your device. Be it browsing through CoinGecko or performing various transactions on different apps, VPNs ensure that your data is encrypted and your location is hidden, preventing external attackers from identifying and attacking the source.
While all VPNs generally do their job of protecting your IP from being exposed, this doesn’t actually stop some of them from collecting your address, should they have a reason to. While no-log VPNs are the current highest standard readily available in the market, users should understand that VPNs are businesses in itself. If a legitimate enforcement request is made by the authorities, it is likely that the company will have no choice but to comply.
 Source: ExpressVPN
Source: ExpressVPN
There is a vast assortment of VPN providers in the market these days, from completely centralized platforms such as ExpressVPN and Atlas VPN to decentralized versions such as Sentinel and Hopr. Each one offers a different range of additional tools and features, which may vary for free and paying users, so be sure to check each one out before deciding which VPN service is the right for you.
2. Changing MetaMask’s RPC Endpoint
If using VPNs isn’t something you’re too keen on, or you want even more privacy assurances, that doesn’t mean that you can’t continue using MetaMask. You may consider switching the default RPC endpoint for the Ethereum mainnet (Infura) to another provider instead.
In 2022, users can now access a variety of free and paid RPC services that come in different price tiers to suit their needs. For a selection of public (but perhaps not so private) RPCs, you can check out a list compiled by DeFiLlama here. Otherwise, paid RPC providers such as Alchemy and QuikNode allow users to get their own private RPC endpoints in order to access the blockchain, and it’s fairly easy to set up in MetaMask. At the moment, MetaMask currently restricts users from changing the endpoint on the default Ethereum mainnet, so you will have to add a new network that also connects to Ethereum but using a different RPC endpoint. This is now scheduled to change in a future update from MetaMask to make it easier.
Step-by-Step Guide to Adding New Networks
-
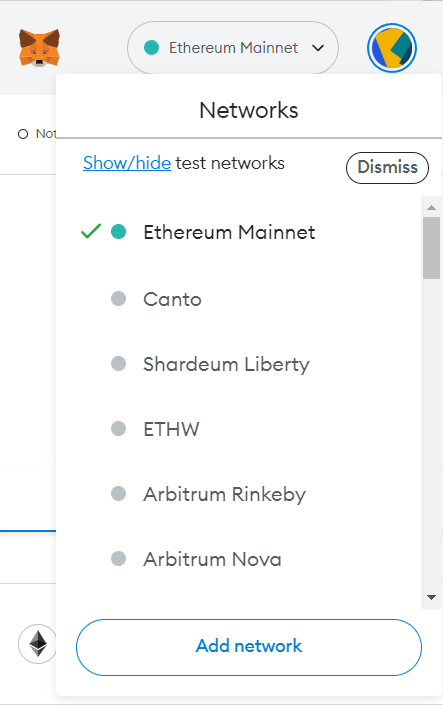
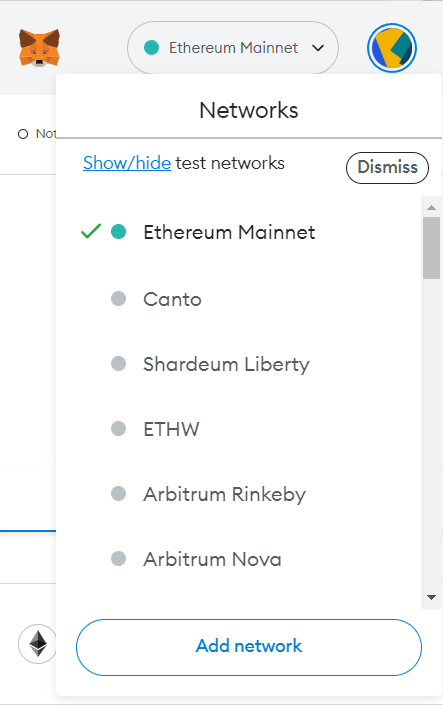
In the MetaMask extension, click on the drop-down tab to open up a list of your current networks and click on ‘Add Network’
-
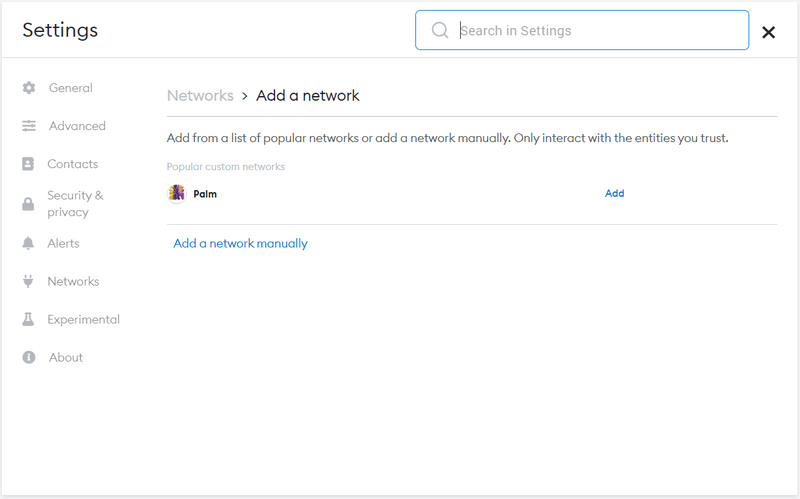
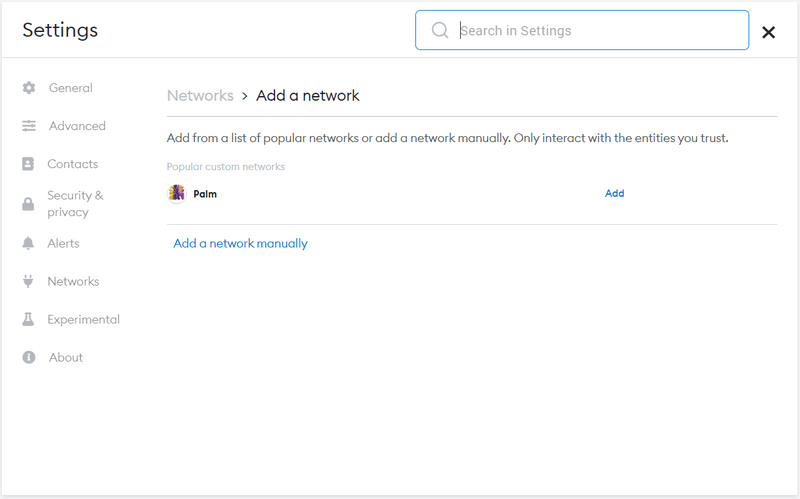
A new tab for the MetaMask extension will then be opened, allowing you to also add pre-existing networks (with a set RPC endpoint) automatically. For this example, we will be adding the network manually.
-
On the next page, you will be prompted to fill in several key details before the network can be successfully added, such as the network’s name, RPC URL, and chain ID. It is recommended that you choose a name that will make it easier to identify that it is the Ethereum network. Copy and paste your RPC URL and enter “1” as the chain ID. Optionally, you may also add a URL to a specific block explorer. Once you’re done, click “Save” and you’re ready to use your new RPC endpoint.

Although moving away from Infura may offer some peace of mind, using a third-party RPC doesn’t really guarantee that your IP address isn’t exposed as well. Each RPC provider will have different terms and conditions in regard to what information they can collect from their users, so it’s important to really dive into the fine print and be aware of what you’re signing up for.
3. Running your own ETH Node
When engaging with centralized entities, there’s always a risk that your personal information may be collected, with or without your knowledge, for malicious purposes. Thus, for a truly decentralized experience, more experienced users may be tempted to spin up their own Ethereum node. Running your own node allows you to transmit your own transactions privately and directly to Ethereum without the risk of censorship by third parties. Your personal node will allow you to host your own RPC endpoints and plug them into MetaMask or any other wallet.
However, running a node requires some level of technical know-how, as well as the appropriate hardware, which could be quite an investment. Despite that, there are several preconfigured plug-and-play options available for beginners, from vendors such as DappNode and Avado, with built-in software right out of the box.
 Source: DappNode
Source: DappNode
Even if you choose to build your own machine, setting up the necessary software to run and manage your node is equally simple, with just a few clicks. Projects such as NiceNode and Stereum offer a user-friendly experience for newbies to easily install their choice of clients to run as well as a control center to monitor and make adjustments to their nodes.
However, users should be aware that connecting a node to the Ethereum network does expose the IP address of your device, although it can’t be associated with you or any particular entity. Regardless, this opens up plenty of opportunities for hackers to find weak spots in your device and infiltrate your system. As such, understanding and taking the neccessary steps to strengthen the security of your node, such as configuring the right firewalls, is a must if you’re headed down this route.
4. Using other Cryptocurrency Wallets
If you don’t really want to continue using MetaMask, switching to other wallet providers is a viable option as well. While MetaMask has been the go-to wallet for the majority of Web3 natives for interacting with EVM blockchains, various new alternatives have sprung up in recent years to challenge the throne. For a non-exhaustive list of wallet providers, you can check out Sov’s Compendium here.
Some of these wallets have proven to be solid options, such as XDEFI and Coin98, and are even besting MetaMask in certain aspects, such as the ability to support non-EVM networks. For users who may want more private or decentralized options, wallets such as Frame and Tally Ho are starting to gain traction and are definitely worth looking into.
 Source: Frame.sh
Source: Frame.sh
However, it’s important to note that other wallets may also be collecting your IP addresses, which defeats the purpose of moving away from MetaMask in the first place. Additionally, each wallet comes with its own UI and offers a very different user experience, which may be unfamiliar to newer crypto participants, making it a bit trickier for them to make the switch. While some wallet providers have tried to tackle this by recreating the familiarity of MetaMask, the overall performance of the wallet itself tends to be subpar for the most part. Unlike MetaMask, which has become the default option for connecting and executing transactions on most dApps, not every wallet may be properly supported.
Conclusion
In a world where ‘everything is for sale’, including sensitive information, it makes complete sense for users to take pains to ensure that their private data remains private. As more companies are becoming increasingly comfortable in promoting “users as the product”, it’s hard to blame users for becoming skeptical and paranoid each time they hear that their data is being collected. Once they’ve been blue-pilled, many understandably go to great lengths to protect their privacy.
Self-sovereignty is the only viable alternative for privacy, and projects in the crypto space are building the tools to give control back to the users. For better or worse, the existence of decentralized networks and the plethora of tools currently available has allowed almost everyone to take ownership of their own security and privacy, lest it is taken advantage of for nefarious purposes. As this incident shows, there are still significant hurdles to surmount, and we all need to remain vigilant and exercise care in mitigating risks across the apps that we use and love.

Win Win is an avid gamer, interested in navigating the vast world of NFTs and the cryptoverse. Entering the crypto space in 2020, Win Win focuses particularly on DeFi and GameFi, looking out for the latest developments and projects in the space. The author has lived through the meteoric rise of DeFi as well as the collapse of Terra and FTX. Follow the author on Twitter @0x5uff3r








 Or check it out in the app stores
Or check it out in the app stores